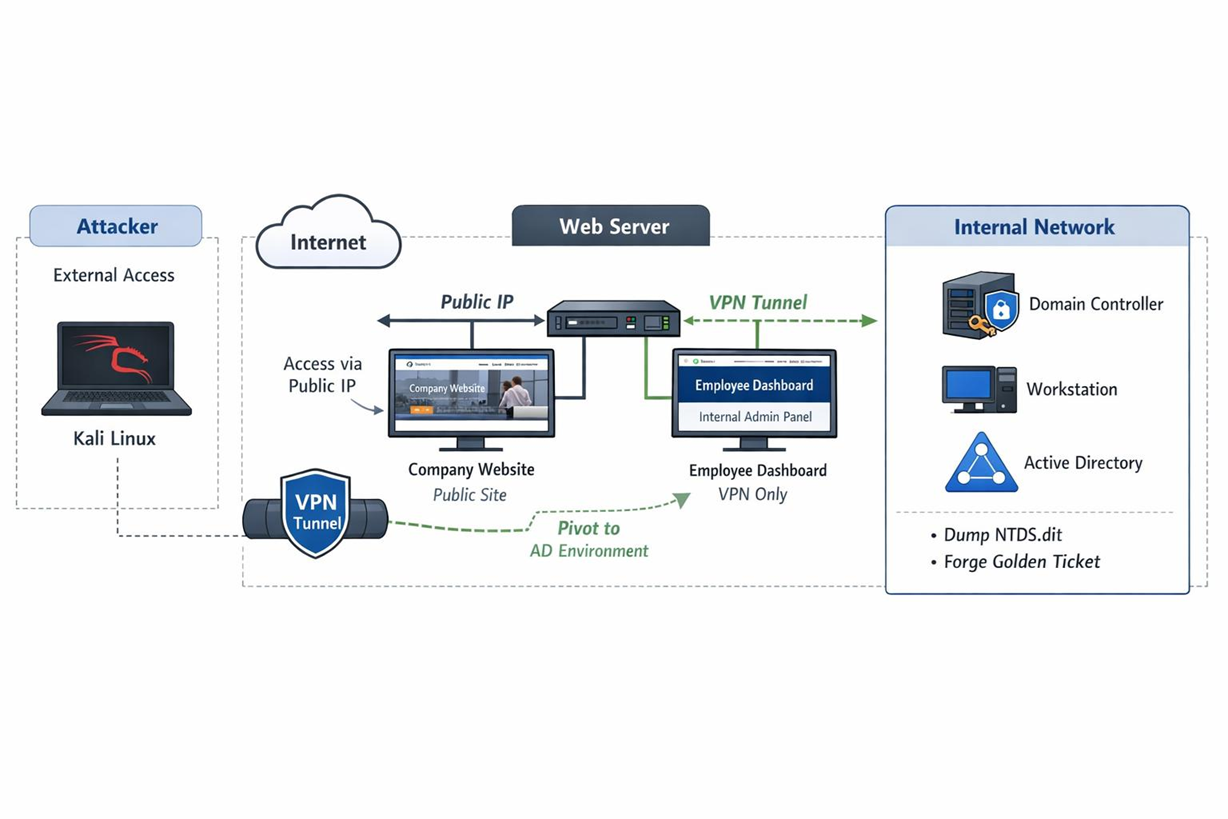
On-Demand Enterprise Network
Full corporate network simulation practice lab
Hands-On Practical Learning
- Web & API Exploitation
- Pivoting and Tunneling
- Internal Network Breach
- Active Directory Initial Access
- Privilege Escalation
- Lateral Movement
- Full Domain Compromise
- Domain Persistence
